https://cryptohack.org/courses/symmetric/aes3/
KeyExpansion階段會將16字節密鑰轉換為11個4x4矩陣,這些矩陣稱為「輪密鑰」(round keys),這些密鑰是從我們的初始密鑰衍生出來的。有了這些輪密鑰,AES可以更有效地利用我們提供的單一密鑰。
接下來是就是初始密鑰添加階段(Initial Key Addition phase),這題就是要介紹AddRoundKey步驟。
AddRoundKey步驟很簡單:它將當前狀態(state)與當前輪密鑰(round key)進行異或(XOR)運算。
(AddRoundKey示意圖)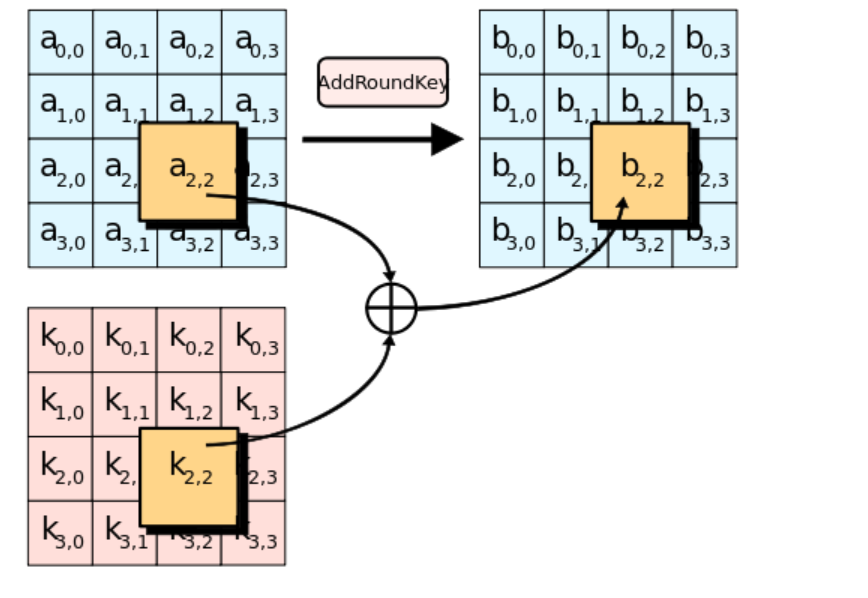
雖然XOR運算極容易還原,但要破解AES加密仍是不容易的,試想不知道密鑰但要還原11個不同密鑰加密過的明文,且每次加密之間還經過一系列複雜的替換和變換,要破解可是不小的工程呢~
我們需要完成 add_round_key 函數,讓當前狀態(state)與當前輪密鑰(round key)進行異或(XOR)運算。
from pwn import xor
state = [
[206, 243, 61, 34],
[171, 11, 93, 31],
[16, 200, 91, 108],
[150, 3, 194, 51],
]
round_key = [
[173, 129, 68, 82],
[223, 100, 38, 109],
[32, 189, 53, 8],
[253, 48, 187, 78],
]
def add_round_key(s, k):
flag=b""
for i in range(4):
for j in range(4):
flag+=xor(s[i][j],k[i][j])
return flag
print(add_round_key(state, round_key))
crypto{r0undk3y}
Forward S-box
Inverse S-box
AES的S-box: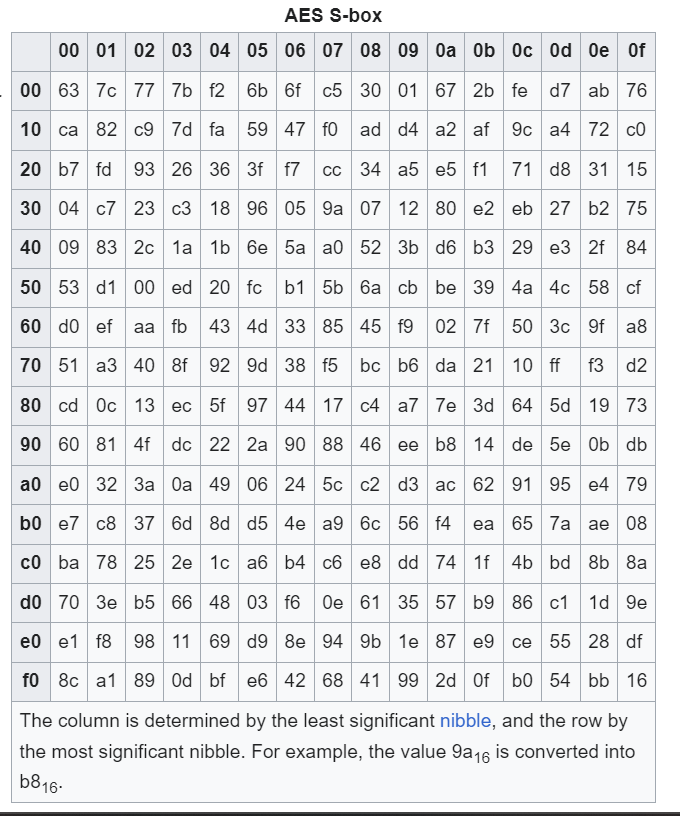
https://cryptohack.org/courses/symmetric/aes4/
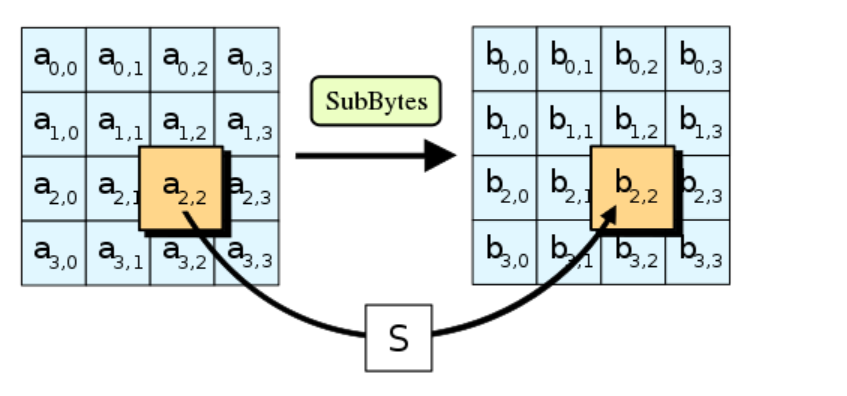
介紹了 SubBytes的步驟、S-box以及混淆性(如上)。
完成 sub_bytes 函數,將狀態矩陣(state)通過反S-box處理,並將其轉換為字節。
s_box的部分解密時用不到,這邊就沒有放上來了。
inv_s_box = (
0x52, 0x09, 0x6A, 0xD5, 0x30, 0x36, 0xA5, 0x38, 0xBF, 0x40, 0xA3, 0x9E, 0x81, 0xF3, 0xD7, 0xFB,
0x7C, 0xE3, 0x39, 0x82, 0x9B, 0x2F, 0xFF, 0x87, 0x34, 0x8E, 0x43, 0x44, 0xC4, 0xDE, 0xE9, 0xCB,
0x54, 0x7B, 0x94, 0x32, 0xA6, 0xC2, 0x23, 0x3D, 0xEE, 0x4C, 0x95, 0x0B, 0x42, 0xFA, 0xC3, 0x4E,
0x08, 0x2E, 0xA1, 0x66, 0x28, 0xD9, 0x24, 0xB2, 0x76, 0x5B, 0xA2, 0x49, 0x6D, 0x8B, 0xD1, 0x25,
0x72, 0xF8, 0xF6, 0x64, 0x86, 0x68, 0x98, 0x16, 0xD4, 0xA4, 0x5C, 0xCC, 0x5D, 0x65, 0xB6, 0x92,
0x6C, 0x70, 0x48, 0x50, 0xFD, 0xED, 0xB9, 0xDA, 0x5E, 0x15, 0x46, 0x57, 0xA7, 0x8D, 0x9D, 0x84,
0x90, 0xD8, 0xAB, 0x00, 0x8C, 0xBC, 0xD3, 0x0A, 0xF7, 0xE4, 0x58, 0x05, 0xB8, 0xB3, 0x45, 0x06,
0xD0, 0x2C, 0x1E, 0x8F, 0xCA, 0x3F, 0x0F, 0x02, 0xC1, 0xAF, 0xBD, 0x03, 0x01, 0x13, 0x8A, 0x6B,
0x3A, 0x91, 0x11, 0x41, 0x4F, 0x67, 0xDC, 0xEA, 0x97, 0xF2, 0xCF, 0xCE, 0xF0, 0xB4, 0xE6, 0x73,
0x96, 0xAC, 0x74, 0x22, 0xE7, 0xAD, 0x35, 0x85, 0xE2, 0xF9, 0x37, 0xE8, 0x1C, 0x75, 0xDF, 0x6E,
0x47, 0xF1, 0x1A, 0x71, 0x1D, 0x29, 0xC5, 0x89, 0x6F, 0xB7, 0x62, 0x0E, 0xAA, 0x18, 0xBE, 0x1B,
0xFC, 0x56, 0x3E, 0x4B, 0xC6, 0xD2, 0x79, 0x20, 0x9A, 0xDB, 0xC0, 0xFE, 0x78, 0xCD, 0x5A, 0xF4,
0x1F, 0xDD, 0xA8, 0x33, 0x88, 0x07, 0xC7, 0x31, 0xB1, 0x12, 0x10, 0x59, 0x27, 0x80, 0xEC, 0x5F,
0x60, 0x51, 0x7F, 0xA9, 0x19, 0xB5, 0x4A, 0x0D, 0x2D, 0xE5, 0x7A, 0x9F, 0x93, 0xC9, 0x9C, 0xEF,
0xA0, 0xE0, 0x3B, 0x4D, 0xAE, 0x2A, 0xF5, 0xB0, 0xC8, 0xEB, 0xBB, 0x3C, 0x83, 0x53, 0x99, 0x61,
0x17, 0x2B, 0x04, 0x7E, 0xBA, 0x77, 0xD6, 0x26, 0xE1, 0x69, 0x14, 0x63, 0x55, 0x21, 0x0C, 0x7D,
)
state = [
[251, 64, 182, 81],
[146, 168, 33, 80],
[199, 159, 195, 24],
[64, 80, 182, 255],
]
def sub_bytes(s, sbox):
flag=""
for i in s:
for j in i:
flag+=chr(sbox[j])
return flag
print(sub_bytes(state, sbox=inv_s_box))
crypto{l1n34rly}
AES進階加密標準:
https://ithelp.ithome.com.tw/articles/10289999?sc=iThelpR
AES加密算法原理介绍:
https://goodapple.top/archives/162
混淆與擴散:
https://zh.wikipedia.org/wiki/%E6%B7%B7%E6%B7%86%E8%88%87%E6%93%B4%E6%95%A3
S盒: https://zh.wikipedia.org/zh-tw/S%E7%9B%92
AES的S盒:
https://en.wikipedia.org/wiki/Rijndael_S-box
這邊已經很多字了,今天先這樣~
